Good news - after weeks of hard work Google developers have brought to us the new Chrome 13. Moreover, we've already installed it at Browserling, ready for your testing needs.
Try it yourself right away!
What's new in Chrome 13?
The most notable features are as follows:
- Instant Pages (pre-rendering of Web pages).
- Native print interface and preview (Linux and Windows only).
- Experimental new tab page.
- Experimental Restrict Instant To Search option.
Instant Pages
Chrome Instant Pages (Not to be confused with Chrome Instant) requires that Chrome itself and the site should support this feature. For instance Google Search. The concept is that when you perform a search in Google, the browser will pre-load the page for the result link you're most likely to click on in the background. The pre-load is actually not only for the base HTML file. Chrome downloads all resources, and even executes javascript before the user clicks on the search result.
Built-in Flash
Currently, Google Chrome is the only browser to come with Adobe Flash built in. Users usually find installing it separately for annoying. Also it will do the updates automatically, because the frequent urge to update Adobe Flash has been equally annoying. Currently for Windows 7 and Vista, the Flash scripts will run in an isolated sandbox so that it doesn't have access to critical system areas. This faced the previously-mentioned security issues with Adobe Flash.
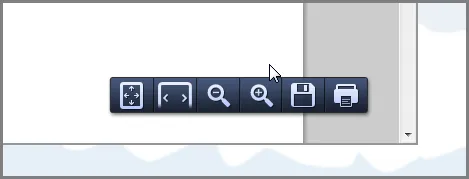
Built-in PDF
There is also a built-in PDFsupport, sparing you the torment of installing some plug-ins to view such a specialized Web content. When you load a PDF, an intuitive toolbar shows when the cursor is in the southeast vicinity of the browser window. There you can choose to execute a variety of different things such as zooming in and zooming out.
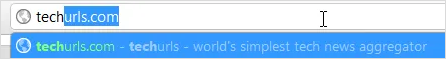
Chrome Instant
This is one of the most anticipated features for Google Chrome to this point. It is their innovative performance solution to pre-load websites as you type their url in the "omnibox" (another name for the address bar). There is still much work to do on this feature, but it's there.
Developer features and updates in Chrome 13
- File System API (Chromium) - With the FileSystem API, a web app can create, read, navigate, and write to a sandboxed section of the user's local file system.
- Navigation Timing API - Allows web applications to access timing information related to navigation and elements.
- Typed Arrays - Buffers for holding binary data and working with WebGL & Audio API:
ArrayBuffer,Float32Array,Int16Array,Uint8Array, etc.) - Web SQL Database - API exposing an SQLite database
Bug fixes in Chrome 13
- CVE-2011-2358: Always confirm an extension install via a browser dialog.
- CVE-2011-2359: Stale pointer due to bad line box tracking in rendering.
- CVE-2011-2360: Potential bypass of dangerous file prompt.
- CVE-2011-2361: Improve designation of strings in the basic auth dialog.
- CVE-2011-2782: File permissions error with drag and drop.
- CVE-2011-2783: Always confirm a developer mode NPAPI extension install via a browser dialog.
- CVE-2011-2784: Local file path disclosure via GL program log.
- CVE-2011-2785: Sanitize the homepage URL in extensions.
- CVE-2011-2786: Make sure the speech input bubble is always on-screen.
- CVE-2011-2787: Browser crash due to GPU lock re-entrancy issue.
- CVE-2011-2788: Buffer overflow in inspector serialization.
- CVE-2011-2789: Use after free in Pepper plug-in instantiation.
- CVE-2011-2790: Use-after-free with floating styles.
- CVE-2011-2791: Out-of-bounds write in ICU.
- CVE-2011-2792: Use-after-free with float removal.
- CVE-2011-2793: Use-after-free in media selectors.
- CVE-2011-2794: Out-of-bounds read in text iteration.
- CVE-2011-2795: Cross-frame function leak.
- CVE-2011-2796: Use-after-free in Skia.
- CVE-2011-2797: Use-after-free in resource caching.
- CVE-2011-2798: Prevent a couple of internal schemes from being web accessible.
- CVE-2011-2799: Use-after-free in HTML range handling.
- CVE-2011-2800: Leak of client-side redirect target.
- CVE-2011-2802: v8 crash with const lookups.
- CVE-2011-2803: Out-of-bounds read in Skia paths.
- CVE-2011-2801: Use-after-free in frame loader.
- CVE-2011-2818: Use-after-free in display box rendering.
- CVE-2011-2804: PDF crash with nested functions.
- CVE-2011-2805: Cross-origin script injection.
- CVE-2011-2819: Cross-origin violation in base URI handling.
Have fun cross-browser testing in Chrome 13!
Email this blog post to your friends or yourself!
Try Browserling!
Enter a URL to test, choose platform, browser and version, and you'll get a live interactive browser in 5 seconds!



 Subscribe to updates!
Subscribe to updates!
 BizSpark
BizSpark